What If Your Lead Tech Quits Tomorrow?
May 9, 2026The Exit Risk: Protecting Your Houston Firm’s Client List from Data Exfiltration
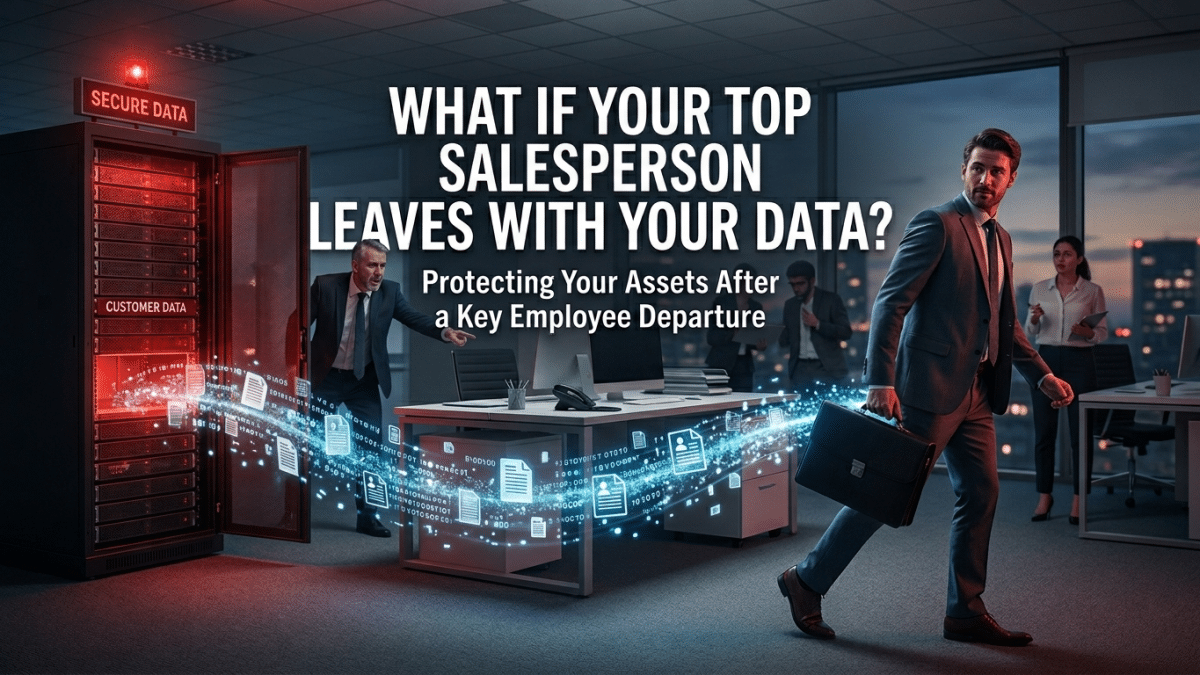
In the competitive landscape of Houston business—where relationships in the Energy Corridor or the Medical Center are worth millions—your client list is your most valuable intellectual property. For years, you have invested in building that database, nurturing leads, and securing contracts. But what happens if your top salesperson decides to move to a competitor and takes your entire CRM with them?
Many owners view this purely as a legal issue. They rely on non-compete agreements and employment contracts. However, in the 2026 digital environment, once the data is gone, the damage is often irreversible regardless of the legal outcome. To protect your firm, you must move beyond the “Legal Shield” and implement a “Technical Shield.”
Protecting your proprietary data requires a strategy that blends visibility, access control, and proactive monitoring. Here is how to ensure that your “competitive edge” doesn’t walk out the door when a salesperson leaves.
The Myth of the “Clean Break”
The most significant risk doesn’t happen on the day an employee gives their notice; it usually happens in the 30 to 60 days before they resign. This is the period of “Data Harvesting.” If an employee has unrestricted access to your CRM or file server, they can slowly download client lists, contract terms, and pricing strategies to personal cloud storage or encrypted USB drives without triggering a single alarm.
If you are only reacting on the day of the exit interview, you are already too late. You need a system that detects “Anomalous Behavior”—such as a salesperson suddenly downloading five years of sales data at 10:00 PM on a Sunday—in real-time.
Closing the “Personal Device” Gap
In the Houston “Commuter Economy,” many sales teams use personal phones or tablets to check emails and update leads. While this offers flexibility, it creates a massive security hole. If your client data is stored locally on a personal device, you have no way to “Remote Wipe” that data once the employee leaves.
To prevent this, businesses must implement Mobile Device Management (MDM) and Containerization. This allows you to separate “Work” data from “Personal” data on a device. When the employee leaves, you can instantly revoke access to the work “container,” effectively deleting your client list from their phone without touching their personal photos or texts.
The “SaaS” Sprawl: Regaining Control of the CRM
One of the most common ways client lists are stolen is through “Export” functions in SaaS platforms like Salesforce or HubSpot. Often, these permissions are left on by default. If your team can export your entire database to a .CSV file with two clicks, your data is not secure.
A robust data protection strategy involves:
- Granular Permissions: Ensuring that sales staff can only see the accounts they are currently managing, rather than the entire company database.
- Export Restrictions: Disabling the ability to export lists unless specifically authorized by management.
- DLP (Data Loss Prevention): Implementing tools that recognize when sensitive information (like phone numbers and email addresses) is being moved to unauthorized locations like personal Gmail accounts or Dropbox.
The “Sentinel” Approach to Offboarding
A departure should be a clinical, technical process. At Krypto IT, we recommend a “Kill Switch” protocol for every Houston firm. This ensures that the moment a resignation is received, the following happens automatically:
- Identity Revocation: All cloud accounts and VPN access are disabled simultaneously.
- Session Termination: Current active sessions on mobile devices and laptops are forcibly ended.
- Redirect Protocols: Client emails are immediately rerouted to a manager to ensure no “final goodbye” messages (carrying a new contact number) are sent to your customers.
Conclusion: Data Security as a Growth Strategy
In the 2026 Trust Economy, your ability to protect your intellectual property is what allows you to scale. If your salespeople know that your data is protected by high-level technical guardrails, it creates a culture of accountability. You aren’t just preventing theft; you are preserving the value of your business.
Is your client list a “walking asset”? Contact Krypto IT today for a “Data Leakage Audit” and let’s secure your competitive advantage.