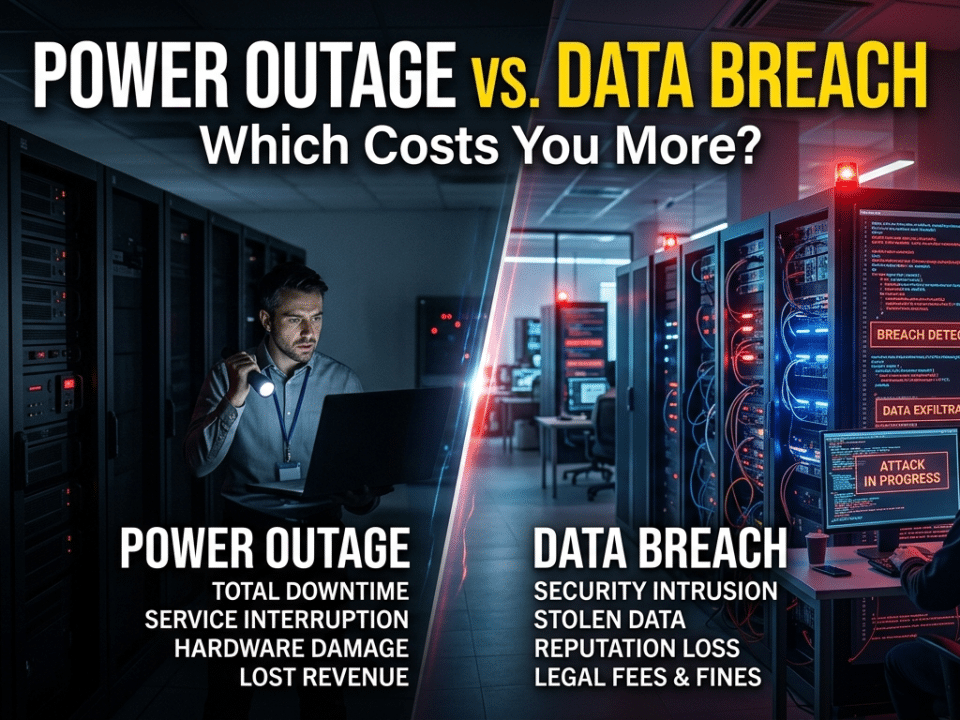
Power Outage vs. Data Breach: Which Costs You More?
May 8, 2026The Single Point of Failure: Is Your Data Tied to One Person’s Memory?
In many Houston businesses—from engineering firms in the Energy Corridor to medical practices in Bellaire—there is often a single individual who “knows how everything works.” We often call this person the Lead Tech, the System Admin, or simply “the person who handles the computers.” They have the passwords, they know the quirks of the server, and they are the only ones who understand why the backup runs at 2:00 AM instead of midnight.
While having a dedicated, knowledgeable expert is an asset, relying on a single person for the entirety of your digital infrastructure creates a “Single Point of Failure” (SPF). If that person were to quit tomorrow, retire, or become unavailable due to an emergency, your business wouldn’t just be losing a staff member—it could be losing access to its most critical data.
To protect your firm’s future, you must move away from a “Person-Centric” IT model and toward a “Process-Centric” one. Here is what happens to your data when a lead tech departs, and how you can prevent a personnel change from becoming a business catastrophe.
The Password Vault Trap
The most immediate crisis following a sudden departure is access. In many firms, passwords are not stored in a centralized, secure vault; they are stored in the Lead Tech’s memory, a personal notebook, or an unencrypted spreadsheet on their local desktop.
If your lead tech leaves on bad terms or is suddenly unreachable, and you do not have the master credentials for your firewall, your domain controller, or your cloud storage, your business is effectively locked out of its own house. You may find yourself forced to perform “hostile” resets of your entire infrastructure—a process that causes massive downtime and carries a high risk of data corruption.
The Documentation Deficit
There is a significant difference between “fixing a problem” and “documenting a solution.” A lone internal tech is often so busy putting out fires that they rarely find the time to document the “wiring” of your network.
When that person leaves, they take their “Tribal Knowledge” with them. They know which cables are loose, which software licenses are about to expire, and which specific workarounds are needed to keep your legacy accounting software running. Without a “Standard Operating Procedure” (SOP) manual, your new hire or external partner will spend weeks—and thousands of dollars in billable time—simply trying to reverse-engineer how your business actually functions.
The Security Risk of the “Quiet Exit”
A departure isn’t always a clean break. If your lead tech has had “the keys to the kingdom” for years, they likely have administrative accounts, remote access tools, and backdoors that you aren’t even aware of.
If you do not have a documented list of every administrative entry point, you cannot effectively “offboard” that individual. This leaves your firm vulnerable to unauthorized access. Even if the departure is friendly, an abandoned administrative account with a weak password is a primary target for external hackers. True security requires a “Kill Switch” capability where one action can revoke access across the entire environment—something that is impossible if your tech was the only one who knew where the accounts were located.
Building Institutional Knowledge
The solution to the “Single Point of Failure” is the creation of Institutional Knowledge. This means that the “how-to” of your business lives within the company’s systems, not within a single employee’s head.
At Krypto IT, we help Houston businesses implement three critical layers of redundancy:
- Centralized Credential Management: Implementing an enterprise-grade password manager where the business owners hold the “Master Keys,” and access is shared with the tech as needed.
- Standardized Documentation Platforms: Using tools that map out every server, every switch, and every software integration in real-time. This ensures that any qualified technician can step in and understand the environment in minutes.
- The Co-Managed IT Model: Partnering your internal tech with an external Managed Service Provider (MSP). This provides your internal person with a “support crew” and ensures that if they are unavailable, the MSP already has the documentation and access needed to keep the business running without missing a beat.
Conclusion: Don’t Let Your Data Be a Hostage
Personnel changes are an inevitable part of doing business in a city as dynamic as Houston. However, your data’s availability should never be tied to a single person’s employment status. Resilience is built on systems, transparency, and documentation.
Is your business one resignation away from a data lockdown? Contact Krypto IT today for a “Continuity Audit” and let’s ensure your company’s knowledge stays where it belongs: with you.