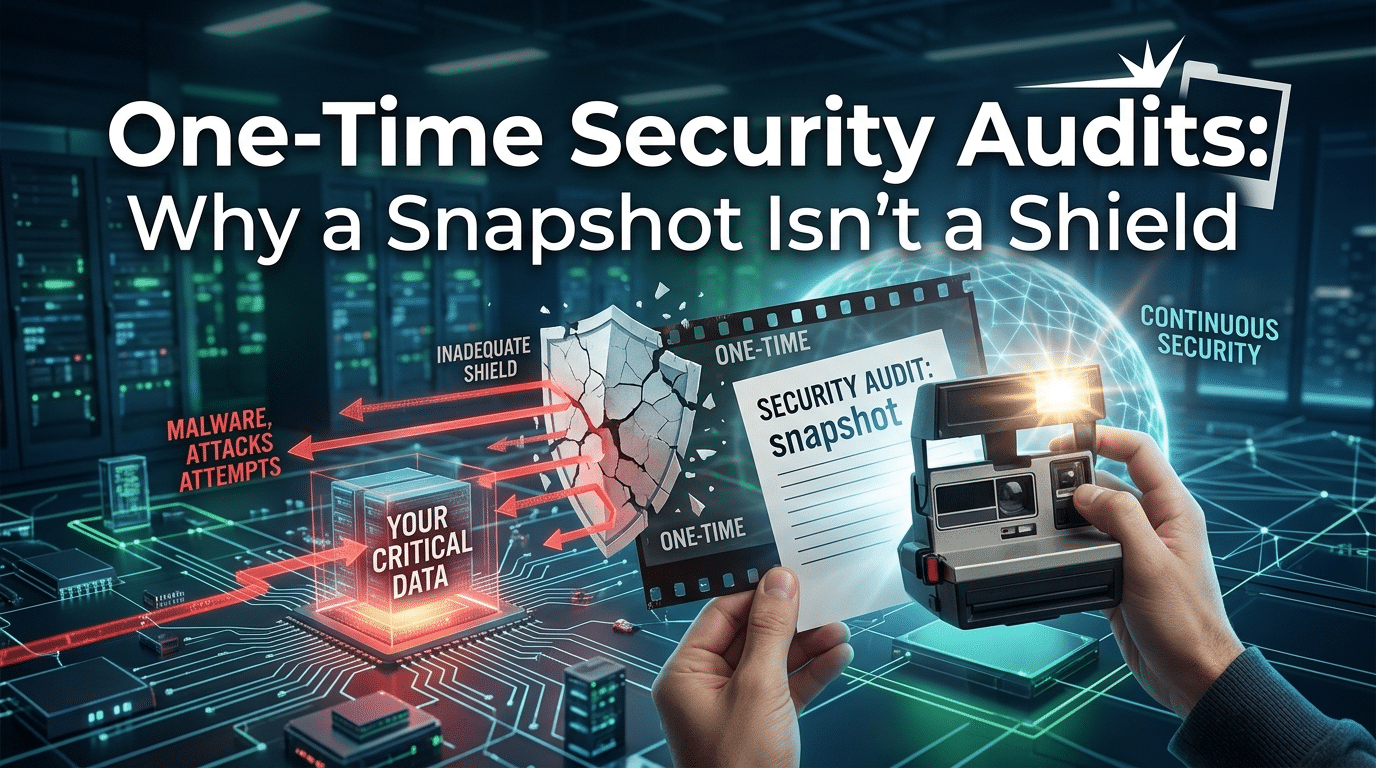
One-Time Security Audits: Why a Snapshot Isn’t a Shield
April 2, 2026Shadow IT in Your Pocket: Why Personal Phone Texting is a Fatal Risk for Houston Firms
Shadow IT Liability Assessment by Krypto IT | Securing Houston’s Mobile Workforce
In the rapid-fire business culture of Houston—from the high-pressure energy trading floors to the fast-moving logistics hubs—the “quick text” has become the default mode of communication. It’s fast, it’s convenient, and everyone has their phone within arm’s reach. But when those texts involve client data, project updates, or internal strategy, and they are sent via a personal device, your firm has entered the dangerous realm of Shadow IT.
At Krypto IT, we recognize that “convenience” is often the enemy of “compliance.” Using personal phones for business texting creates a fragmented, unmanaged, and insecure communication layer that sits entirely outside your firm’s defensive perimeter. This assessment outlines why your “Pocket IT” is a liability waiting to happen.
1. The Shadow IT Fragmentation Index
When business communication happens on personal devices, your corporate intelligence is no longer centralized. It is scattered across dozens of unmanaged hardware units.
As your Shadow IT Fragmentation Index increases, your firm’s ability to protect, audit, and retrieve its own information approaches zero. If a key employee leaves your firm today, do they take your client relationships and project history with them in their “Messages” app? If the answer is “yes,” you don’t own your data; they do.
2. The Legal Discovery Nightmare
In 2026, the “Privacy” of a personal phone ends where a legal “Hold” begins. If your Houston firm is involved in litigation—a common occurrence in construction, law, and oil and gas—the court may demand access to all communications related to a case.
The Liability Reality:
- Intrusive Discovery: If business is conducted on personal phones, those personal phones may become subject to legal “Imaging.” This means a third-party forensic team could potentially scan an employee’s entire device—including private photos and family messages—to find business-related texts.
- The Spoliation Risk: If an employee deletes a text thread on their personal phone that was relevant to a legal matter, your firm could be accused of “Spoliation of Evidence.” This can lead to massive sanctions and a “negative inference” that can lose you the case before it even goes to trial.
3. The “Exfiltration” Backdoor
Personal phones lack the Endpoint Detection and Response (EDR) that Krypto IT installs on your corporate machines. They are often unpatched, running “jailbroken” software, or connected to unsecured public Wi-Fi at a Houston coffee shop.
The Assessment Findings:
- No Malware Filtering: Personal texting apps don’t scan for malicious links or “Smishing” (SMS Phishing) attacks. A single click on a “Project Update” link that turns out to be a credential-stealer can compromise the user’s corporate login stored on that same device.
- No Remote Wipe: If a personal phone is lost or stolen in a busy area like the Galleria, your firm has no way to remotely wipe the sensitive business data contained in those text threads. Your “Shadow IT” is now in the hands of a stranger.
4. The Compliance Gap (HIPAA, FINRA, & Beyond)
For our partners in the Texas Medical Center or the financial districts, the use of personal texting is often a direct violation of federal law. HIPAA and FINRA require that all communications involving sensitive data be encrypted, auditable, and archived. Standard SMS (Green Bubbles) is none of these things.
A “quick text” about a patient’s lab results or a client’s trade instruction isn’t just a security risk; it’s a fine-generating event that can cost your firm its license.
How Krypto IT Professionalizes Your Mobile Strategy
We don’t just “ban” texting; we provide a professional, secure alternative. Krypto IT eliminates the “Shadow IT Trap” through:
- Managed UCaaS (Unified Communications): Providing a professional business number that lives in an app on the employee’s phone, keeping “Work” and “Life” entirely separate and encrypted.
- Centralized Archiving: Ensuring that every business text is logged and searchable for legal and compliance purposes, regardless of who sent it.
- Mobile Device Management (MDM): Implementing “Containerization” that creates a secure, encrypted “Vault” for business apps on personal devices, allowing us to wipe only the business data if a phone is lost.
- Identity-Based Access: Ensuring that if an employee is terminated, their access to the business texting app is cut off instantly, preserving your firm’s data ownership.
Conclusion: Professionalism is the Best Defense
In 2026, the most resilient Houston firms are the ones that have reclaimed their data from the “Shadows.” Convenience should never come at the cost of your firm’s security or legal standing.
Is your firm’s data “Hiding” in your employees’ pockets? Contact Krypto IT today for a “Mobile Liability Audit” and let’s professionalize your communication.