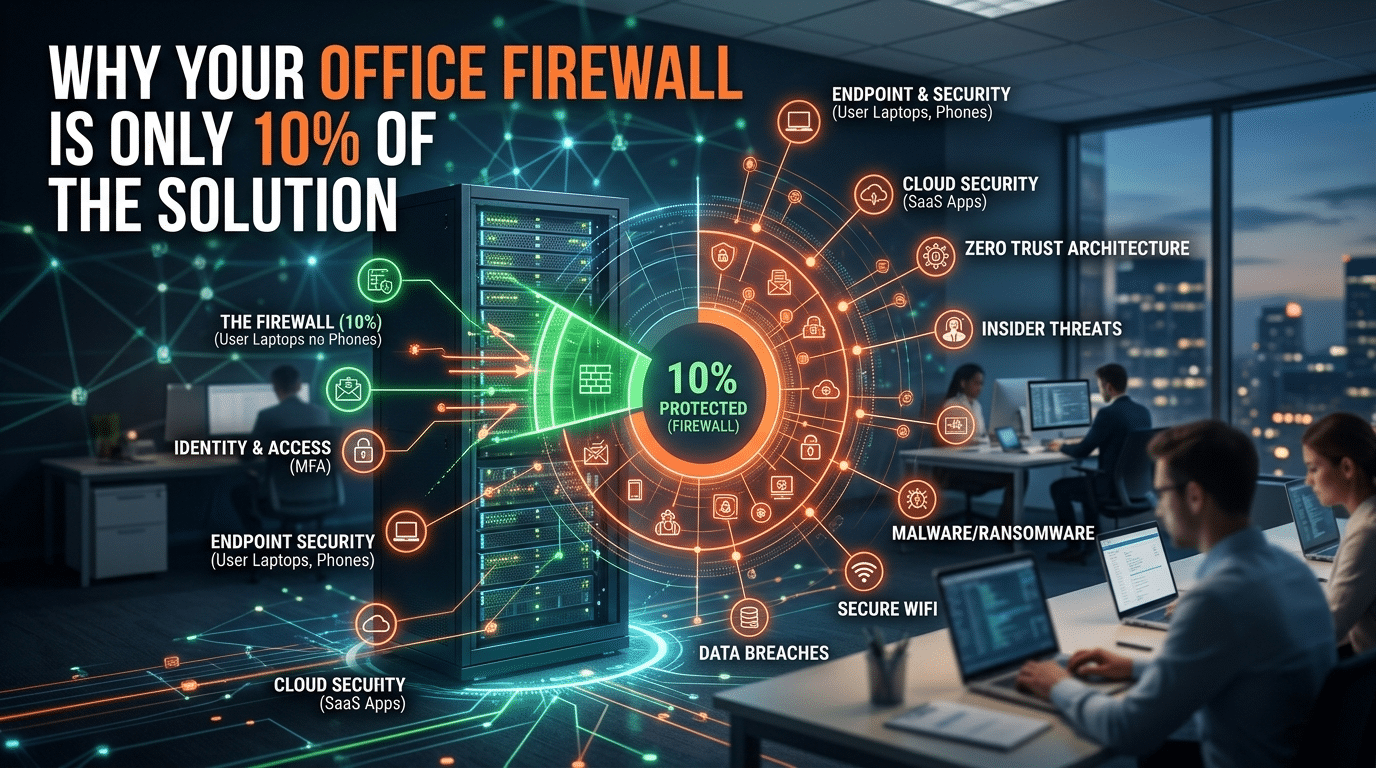
Why Your Office Firewall Is Only 10% of the Solution
April 5, 2026
Rethinking Passwords: Why the 90-Day Rule Fails
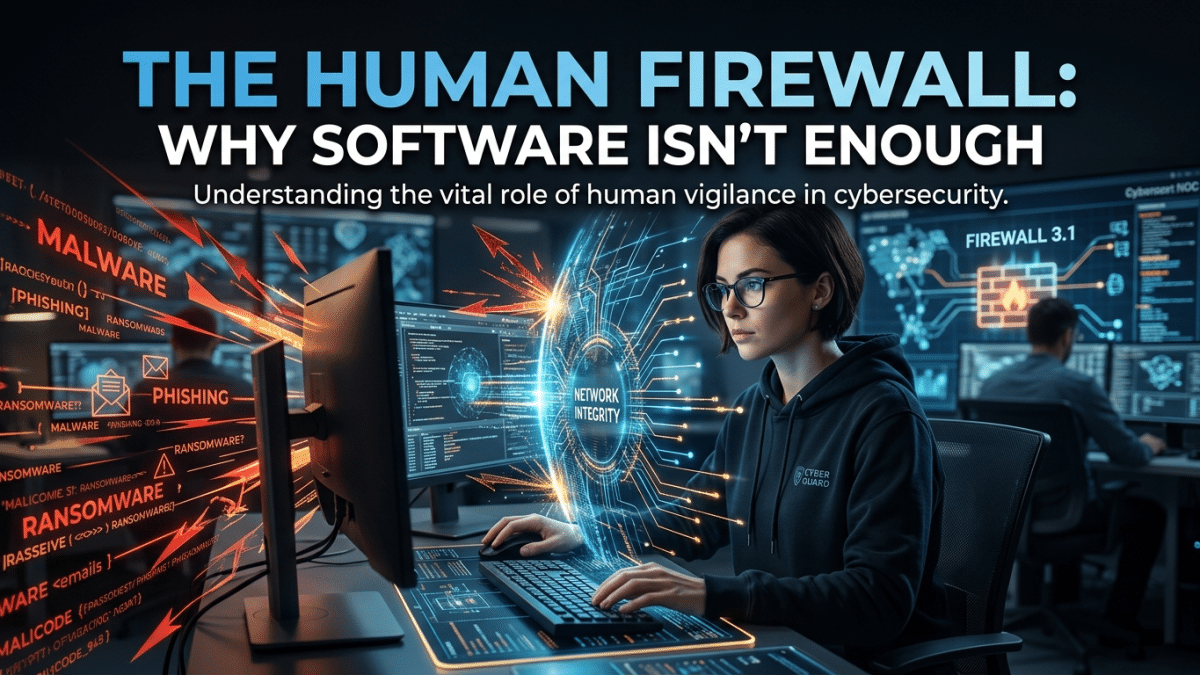
April 8, 2026Beyond the Code: Why the ‘Human Firewall’ is Your Firm’s Ultimate Line of Defense
Behavioral Risk & Cultural Audit by Krypto IT | Hardening the Human Element of Houston’s Economy
In the gleaming offices of Houston’s Energy Corridor and the high-stakes law firms of Downtown, a “Shiny Object” syndrome has taken hold. Organizations are spending millions on the latest AI-driven EDRs, next-gen firewalls, and encrypted cloud clusters. They have built a digital fortress of titanium and steel. But as they admire their walls, they often forget the person holding the keys.
At Krypto IT, we’ve seen the same story play out across Texas: a company buys the best software money can buy, only to be taken down by a single “click” from a tired employee on a rainy Tuesday. In 2026, software is mandatory, but it isn’t a silver bullet. This audit outlines why your “Human Firewall” is your actual first and last line of defense.
1. The Human Vulnerability Index V/h
Cybercriminals no longer spend weeks trying to “crack” a 256-bit encryption. They spend hours trying to “crack” a human brain. In 2026, the path of least resistance is almost always a person, not a port.
If you have a CFO with high “Level of Access” but low “Security Awareness Saturation,” your V/h is off the charts. A software patch cannot fix a CFO who believes a deepfake audio clip of the CEO asking for an urgent wire transfer. To lower your V/h, you must increase the “Saturation” of security culture until it becomes a reflex.
2. Social Engineering 2.0: Hacking the Emotions
In the 2026 threat landscape, hackers aren’t just sending “Nigerian Prince” emails. They are using Generative AI to craft perfect, personalized lures. They study your LinkedIn profile, your company’s press releases, and your industry jargon to create a “Psychological Exploit.”
The Cultural Audit Findings:
- The Urgency Trap: Hackers use fake “Internal HR” notices about payroll errors or “IT Help Desk” alerts about account lockouts. They trigger fear and urgency, which causes the human brain to bypass its logical security training.
- The Curiosity Exploit: “Found these photos from the Houston Holiday Party!” — a simple link that bypasses a million-dollar firewall because it appeals to the human desire for social connection.
Software can scan the link, but it cannot stop the user from typing their credentials into a “look-alike” login page. Only a trained, skeptical mind can do that.
3. The “Set and Forget” Fallacy: Software vs. Brainware
Software is updated automatically. Humans are not. A “One-Time Training Session” held in January is functionally useless by July. The threat landscape moves too fast for annual videos and “check-the-box” quizzes.
The Resilience Standard: A true “Human Firewall” requires Continuous Brainware Updates. At Krypto IT, we implement ongoing, bite-sized training and Simulated Phishing Attacks. We don’t do this to “catch” employees, but to build “Muscle Memory.” When an employee sees a suspicious email, they shouldn’t have to remember a video from six months ago; they should feel a reflexive “red flag” based on their most recent simulation.
4. Shadow IT and the “Convenience Over Security” Culture
When your security software is too restrictive, your “Human Firewall” will find a way around it. This is the birth of Shadow IT. Employees will use personal Dropbox accounts to move files, or unapproved AI tools to summarize meetings, simply because it’s “easier.”
Krypto IT audits the “Friction” in your firm. If your security creates too much friction, your culture will eventually erode your technology. We help Houston firms build a “Secure-by-Default” culture where the right way to do things is also the easiest way.
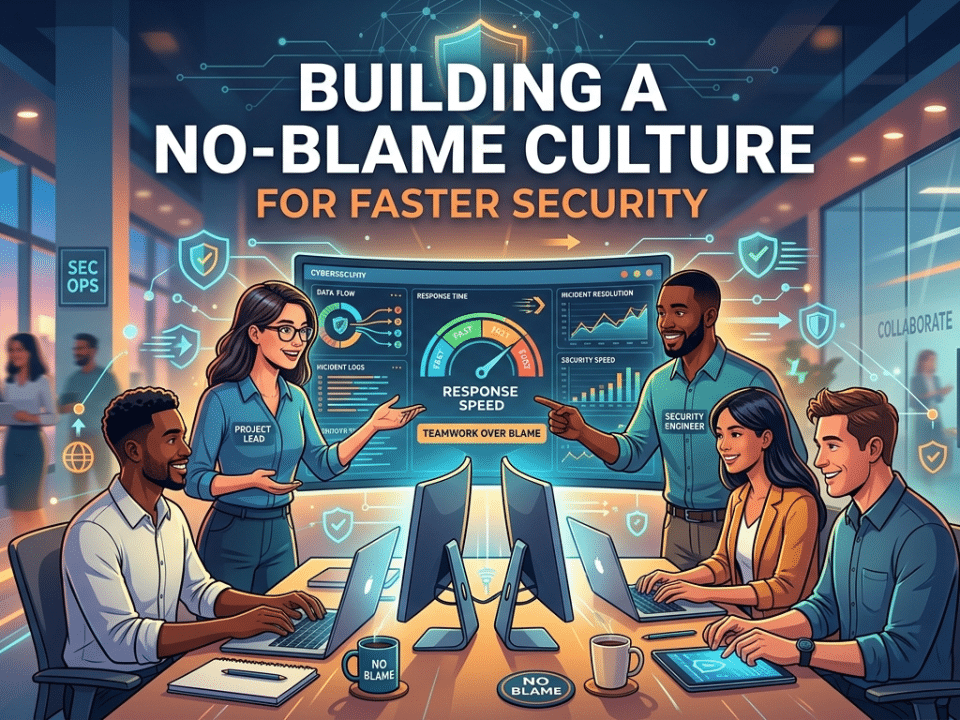
How Krypto IT Hardens Your Human Firewall
We don’t just “manage your patches”; we transform your culture. Krypto IT completes your security stack by focusing on the “Wetware”:
- Managed Awareness Programs: Automated, industry-specific training that evolves with the 2026 threat landscape.
- Simulated Social Engineering: Testing your team with realistic (but safe) lures to identify high-risk users before the hackers do.
- Executive Threat Briefings: Helping your C-Suite understand the specific deepfake and spear-phishing risks targeting Houston’s leadership.
- Cultural Security Alignment: Tuning your technical controls so they support—rather than hinder—your team’s productivity.
Conclusion: The People are the Perimeter
In 2026, the “Perimeter” isn’t a line of code in a firewall; it’s the collective judgment of your employees. Software is your armor, but your people are the ones wearing it. If they don’t know how to buckle the straps, the armor is useless.
Is your “Human Firewall” currently full of holes? Contact Krypto IT today for a “Cultural Security Audit” and let’s turn your team into your greatest asset.