The Shadow IT Trap: Dangers of Business Texting
April 2, 2026
The Human Firewall: Why Software Isn’t Enough
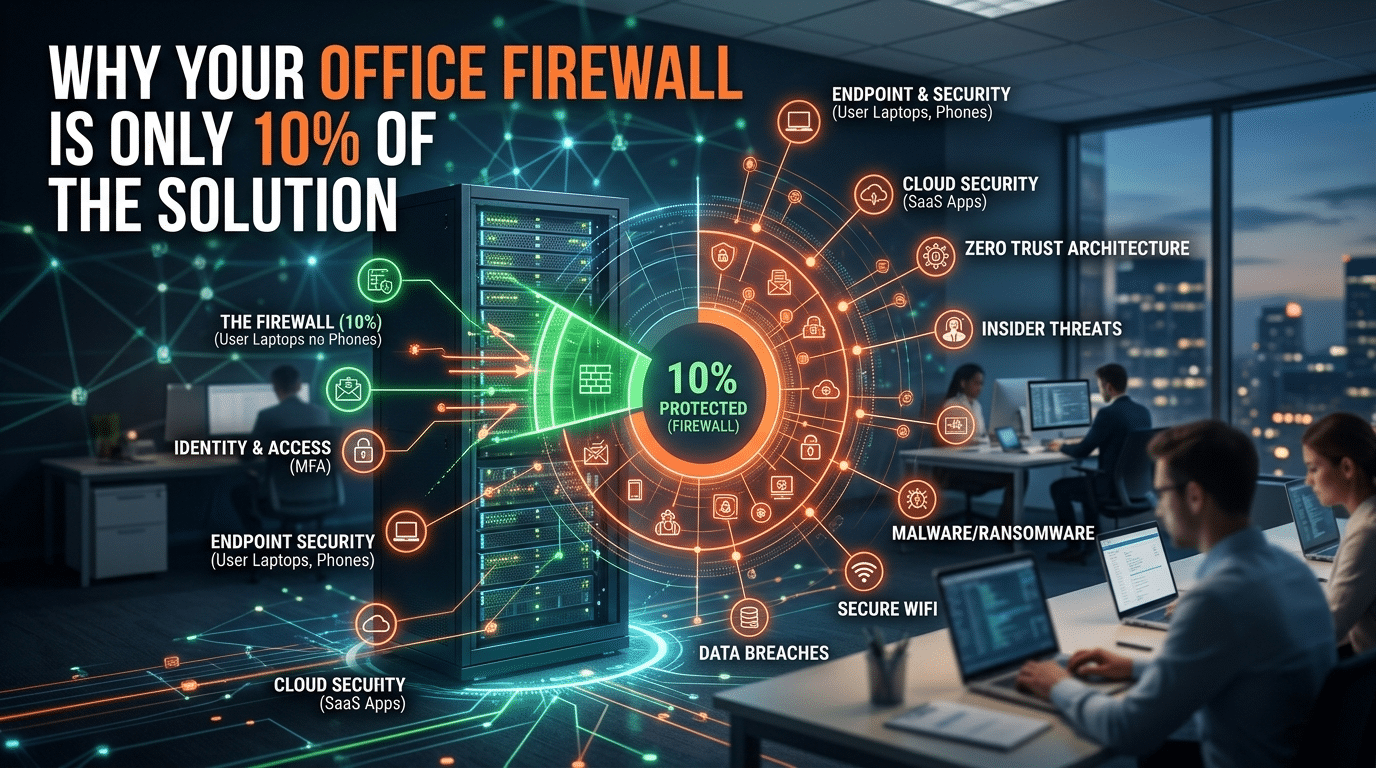
April 7, 2026Beyond the Black Box: Why the Office Firewall is Only 10% of Your 2026 Security
Network Architecture & Perimeter Analysis by Krypto IT | Redefining Defense for Houston’s Hybrid Workforce
In the traditional IT era of Houston—when the “office” was a physical fortress in Greenspoint or Westchase—the firewall was the undisputed king of security. It was the “Great Wall” that separated your trusted internal network from the wild, untrusted internet. If you had a high-end Cisco or Fortinet box humming in your server room, you were “secure.”
At Krypto IT, we are seeing a catastrophic disconnect in 2026. Many Houston firms are still spending 90% of their security budget on that 10% of the solution. In a world of cloud applications, remote work, and identity-based attacks, the firewall has become a “perimeter around an empty field.” This analysis outlines why the “Castle Wall” strategy is dead and what a complete 100% solution actually looks like.
1. The Perimeter Dissolution Index PDI
In 2026, your data doesn’t live behind your firewall. It lives in Microsoft 365, Salesforce, and AWS. Your employees don’t sit behind your firewall; they sit in home offices in Katy, coffee shops in the Heights, and hotels in Dubai.
As your PDI increases, the relevance of your office firewall decreases. If 80% of your company’s work happens in the cloud and on remote devices, your office firewall is only inspecting the remaining 20% of “internal” traffic (like printing or local file sharing). You are effectively guarding the front door of a building while everyone is entering and exiting through the windows and the roof.
2. The “Credential over Code” Shift
A firewall is designed to stop “malicious code” from entering your network. It looks for viruses, worms, and known attack patterns. But in 2026, hackers aren’t “breaking in” with code; they are “logging in” with stolen credentials.
The Architecture Reality: When a hacker steals an employee’s password via a phishing site, they are a “legitimate user” in the eyes of your firewall. The firewall sees an authorized login and opens the gate. A firewall cannot detect that a user’s behavior is malicious if the user has the right “keys.” To stop this, you need Identity and Access Management (IAM) and Conditional Access, which sit far beyond the capabilities of a standard office firewall.
3. Lateral Movement: The “Eggshell” Problem
Most office networks are designed like an egg: a hard outer shell (the firewall) and a soft, unprotected center. Once a threat gets past that 10% perimeter—whether through a compromised laptop brought into the office or a malicious USB drive—it has “Lateral Freedom.”
The Analysis Findings:
- Flattened Networks: We frequently find Houston firms where every device can “see” every other device. If a printer is hacked, the hacker can move laterally to the CEO’s workstation.
- The Missing 90%: To prevent this, you need Micro-Segmentation and Endpoint Detection and Response (EDR). These tools act as “internal firewalls” around every single device, ensuring that even if one “room” is compromised, the rest of the “house” remains locked.
4. The 24/7 Sentinel vs. The Static Filter
A firewall is a static filter. It follows a set of rules (e.g., “Don’t let traffic from Russia in”). But hackers are dynamic. They change their IP addresses, their tactics, and their timing every hour.
A firewall is only 10% of the solution because it lacks Intelligence. It can see that a packet of data is moving, but it doesn’t know why or if that movement is part of a larger, multi-stage attack. To achieve the other 90%, you need the Krypto IT Sentinel Standard—a 24/7 Security Operations Center (SOC) that uses AI and human expertise to monitor behaviors, not just “rules.”
How Krypto IT Builds the Other 90%
We don’t just “install a box”; we architect a fortress. Krypto IT completes your security posture through:
- Zero Trust Architecture: Moving away from “Location-Based” trust to “Identity-Based” trust.
- MDR (Managed Detection and Response): Active threat hunting on every laptop, phone, and server, regardless of where they are located.
- Cloud Governance: Securing your data in M365 and AWS with the same rigor you used for your old server room.
- Security Awareness Training: Hardening your “Human Firewall”—the people who hold the keys to the kingdom.
Conclusion: Foundations Aren’t Houses
A foundation is 10% of a house. You wouldn’t move your family into a home that only had a foundation and no walls, roof, or locks. Your firewall is a foundation, but it is not a complete home for your data.
Is your Houston firm relying on a 10% solution? Contact Krypto IT today for a “Full-Stack Perimeter Analysis” and let’s build a defense that actually works in 2026.