Why Your Brother-in-Law Shouldn’t Run Your IT
March 30, 2026Beyond the Horizon: Debunking the “Set It and Forget It” Cloud Security Myth
Cloud Compliance & Governance Briefing by Krypto IT | Securing Houston’s Modern Infrastructure
In the modern Houston business landscape—from the cloud-native startups in Downtown to the legacy firms migrating their archives in Westchase—there is a dangerous, comforting lie being told in the boardroom: “We moved everything to Microsoft 365 and AWS, so we’re 100% safe. Security is their problem now.”
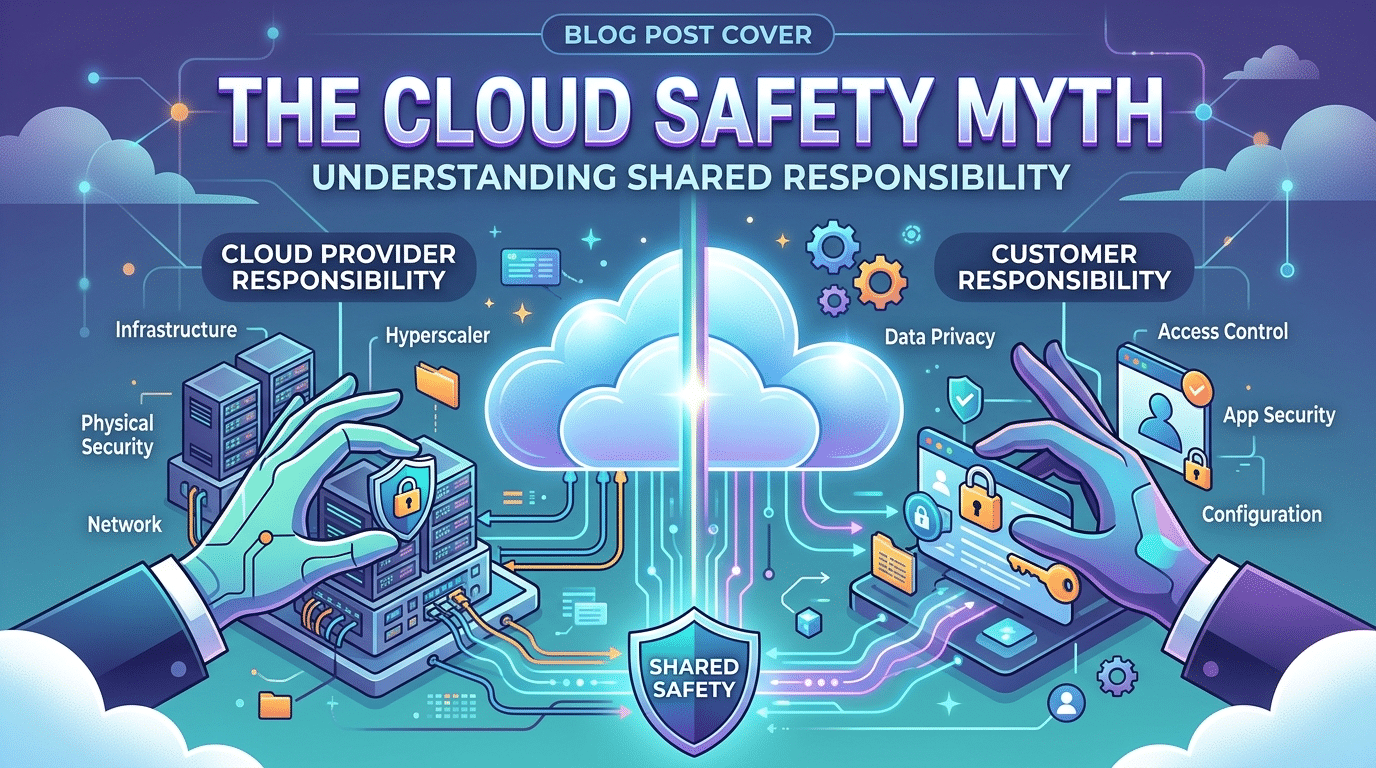
At Krypto IT, we call this the “Cloud Immunity Illusion.” While it is true that a provider like Microsoft or Amazon spent billions on physical security for their data centers, they didn’t secure your data. They secured the “building,” but you still own the “lock” and the “keys.” This briefing outlines the Shared Responsibility Model and why assuming the cloud is a fortress is the fastest way to a breach in 2026.
1. The Shared Responsibility Formula
Cloud security is not a hand-off; it is a partnership. If you don’t understand the line where your provider’s duty ends, you are operating with a “Security Gap” that hackers are eager to exploit.
In 2026, the provider is responsible for the “Security OF the Cloud”—the hardware, the cooling, and the physical perimeter. You are responsible for the “Security IN the Cloud”—your users, your passwords, your permissions, and your data backups. If your Shared Responsibility is unbalanced because you’ve neglected your half of the equation, the “cloud” won’t save you.
2. The “Configuration Overlook”: Why 99% of Cloud Breaches Happen
Gartner famously predicted that through 2026, 99% of cloud security failures will be the customer’s fault. This isn’t because the software is bad; it’s because the “switches” were left in the wrong position.
The Governance Audit Findings:
- Over-Privileged Users: We frequently find Houston firms where every employee has “Global Admin” rights in Microsoft 365. This is the equivalent of giving every tenant in an apartment building a master key to every other unit.
- Publicly Accessible S3 Buckets: In AWS, it is shockingly easy to leave a data folder “public” by mistake. Hackers use automated scrapers to find these “open doors” every single day.
- Legacy Protocol Vulnerability: Many firms migrate to the cloud but leave “Legacy Authentication” turned on for old devices. This creates a backdoor that bypasses modern security measures like MFA.
3. The “Trash Can” Myth: Why You Still Need Backups
Many Houston owners believe that because their data is in OneDrive or Google Drive, it is “backed up.” This is a fatal misunderstanding of Syncing vs. Backing Up.
If a user in your Katy office accidentally deletes a critical project folder, or if a ransomware strain encrypts your local files and “syncs” that encryption to the cloud, your cloud provider is simply doing its job: mirroring the change. They don’t keep an infinite “undo” button for your mistakes. Without an independent, third-party backup of your cloud data, a single “Delete” click can become a permanent data loss event.
4. Identity is the New Perimeter
In the 2026 “Work from Anywhere” Houston economy, your office walls are no longer your security perimeter. Your users’ identities are the perimeter. If a hacker steals an employee’s password via a phishing site at a coffee shop in Memorial, they aren’t “hacking the cloud.” They are “logging in” as a legitimate user. The cloud provider sees this as a valid entry. Without Conditional Access Policies—which look for anomalies like “impossible travel” (logging in from Houston and then five minutes later from London)—the cloud provider will let the intruder in every time.
How Krypto IT Hardens Your Cloud Presence
We don’t just “move you to the cloud”; we build the “Sentinel” around it. Krypto IT secures your cloud infrastructure through:
- Cloud Configuration Audits: We find the “open switches” and over-privileged accounts before a hacker does.
- Independent Cloud Backups: Providing a “Siloed” copy of your data that exists outside of your primary cloud provider.
- Identity Governance: Implementing Zero Trust and Conditional Access so that only the right people get in, from the right places, at the right times.
- Active Threat Hunting: Our SOC monitors your cloud logs 24/7 for the “quiet” signs of an intruder sitting in your tenant.
Conclusion: Ownership is the Foundation of Safety
The cloud is a powerful tool, but it is not a shield. In 2026, the most secure businesses in Houston are the ones that take full ownership of their data governance.
Is your “Shared Responsibility” currently a “Shared Risk”? Contact Krypto IT today for a “Cloud Governance Audit” and let’s secure your digital horizon.