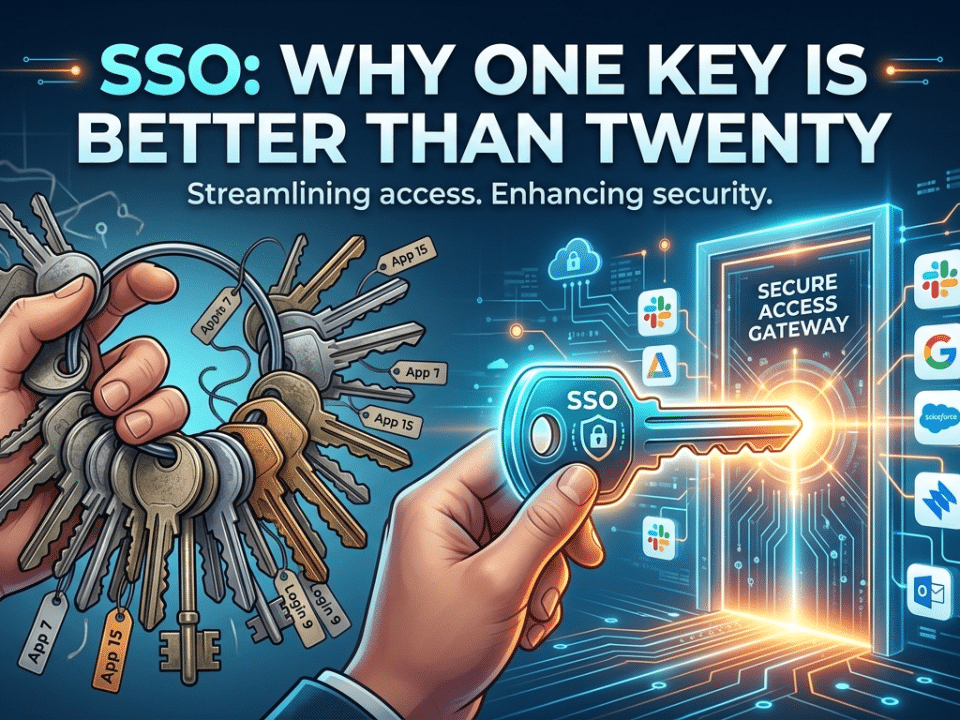
SSO: Why One Key is Better Than Twenty
April 16, 2026Darkness in the Data: Why the Apps You Don’t Know About are Killing Your Security
The Contrarian’s Security Playbook by Krypto IT | Challenging Outdated IT Dogma in Houston
If you run a business in Houston—whether you’re managing a legal team in Downtown or a logistics hub near the Ship Channel—you likely feel a sense of pride in your “Official” tech stack. You’ve invested in Microsoft 365, you have a professional CRM, and your firewall is humming in the server room. You believe you know exactly where your data is.
At Krypto IT, we have some uncomfortable news for you: Your most sensitive company data is likely currently sitting in a personal Dropbox account, a random AI summarizing tool, or a “free” file-conversion website that you never authorized.
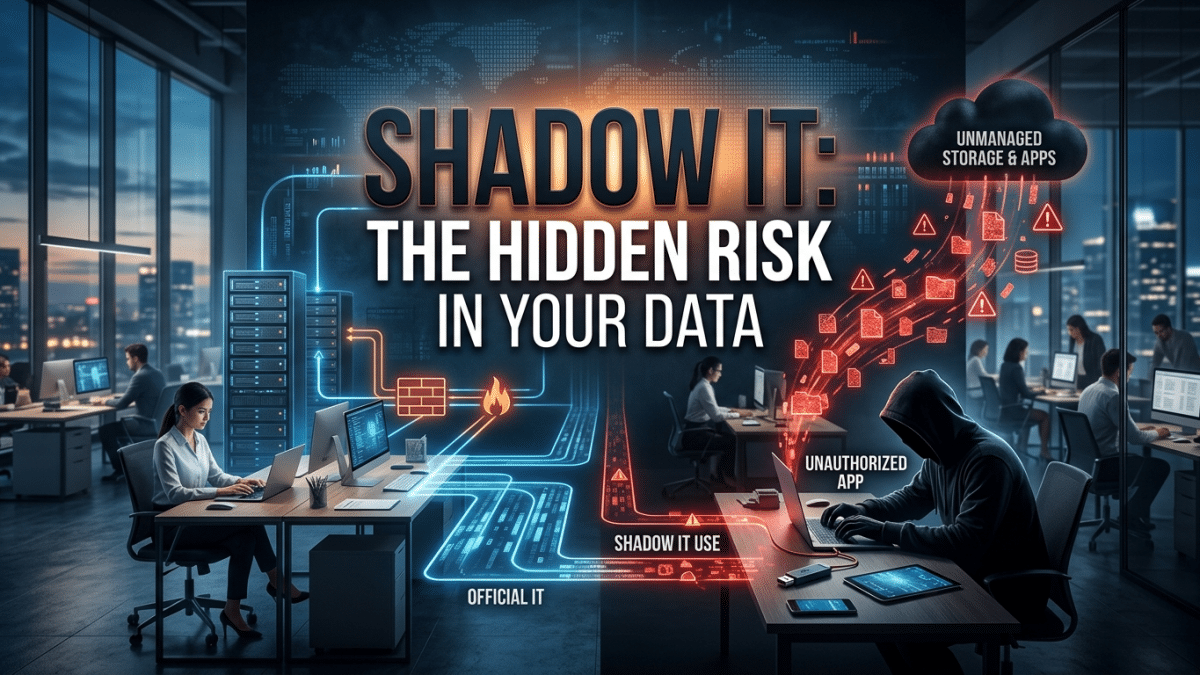
This is Shadow IT. It is the “darkness in your data,” and in 2026, it is the single biggest hurdle to achieving true security. But here is the contrarian truth: Your employees aren’t using these tools to be malicious; they are using them because your “official” IT is too slow, too clunky, or too restrictive.
The “Helpful” Employee: Your Biggest Security Leak
The traditional view of a data breach involves a hacker in a hoodie. The reality of Shadow IT involves a “star employee” who just wants to get their work done before the 5:00 PM deadline.
Imagine your lead engineer in Sugar Land needs to send a massive CAD file to a contractor. Your official file-sharing tool is slow and requires a three-step authentication process. So, they just upload it to their personal WeTransfer or Google Drive.
The Risk: The moment that file hits a personal account, it is gone. It is no longer under your “Sentinel” umbrella. If that employee leaves your firm, that proprietary design stays in their personal cloud. If their personal account is hacked—which lacks your firm’s enterprise-grade MFA—your “Secret Sauce” is now for sale on the dark web. Shadow IT is the process of your company’s intellectual property “leaking” out of your control, one “convenient” click at a time.
The AI Explosion: Shadow IT 2.0
In 2026, the biggest driver of Shadow IT is Generative AI. Your marketing team is likely using “free” AI tools to draft copy. Your HR team might be using unapproved AI note-takers to summarize sensitive interviews.
The Contrarian View: You might think you’re “innovating,” but if you haven’t provided an enterprise-grade, secure AI environment, your staff is feeding your corporate secrets into public AI models. Many of these free tools retain the data you feed them to “train” the model. You are effectively donating your proprietary data and client secrets to the public domain in exchange for a 10-minute time-save.
Why “Banning” is a Losing Battle
The old-school IT response to Shadow IT was to play a game of “Whack-a-Mole.” As soon as IT found an unapproved app, they blocked it on the firewall.
At Krypto IT, we know this doesn’t work. In the age of 5G and personal hotspots, an employee who feels blocked will simply switch to their personal phone or home network to get the job done. Banning doesn’t stop the behavior; it just drives the behavior further into the darkness where you can’t see it.
The real solution isn’t to say “No”; it’s to ask “Why?” If your team is using an unapproved messaging app, it’s because your official one is failing them. Shadow IT is a “User Experience” problem masquerading as a security problem.
The Krypto IT “Illumination” Strategy
We don’t believe in blind bans. We believe in Visibility and Enablement. Krypto IT tackles the darkness by shining a light on your network:
- Cloud App Discovery: We use advanced monitoring tools to identify every single third-party app currently interacting with your data. We show you the “Shadow” map of your company so you can see where the leaks are.
- The “Paved Path” Policy: We work with you to find secure, enterprise-grade alternatives to the tools your team loves. If they need AI, we give them a secure, private AI instance. If they need fast file sharing, we optimize your official tools so there’s no “friction” to bypass them.
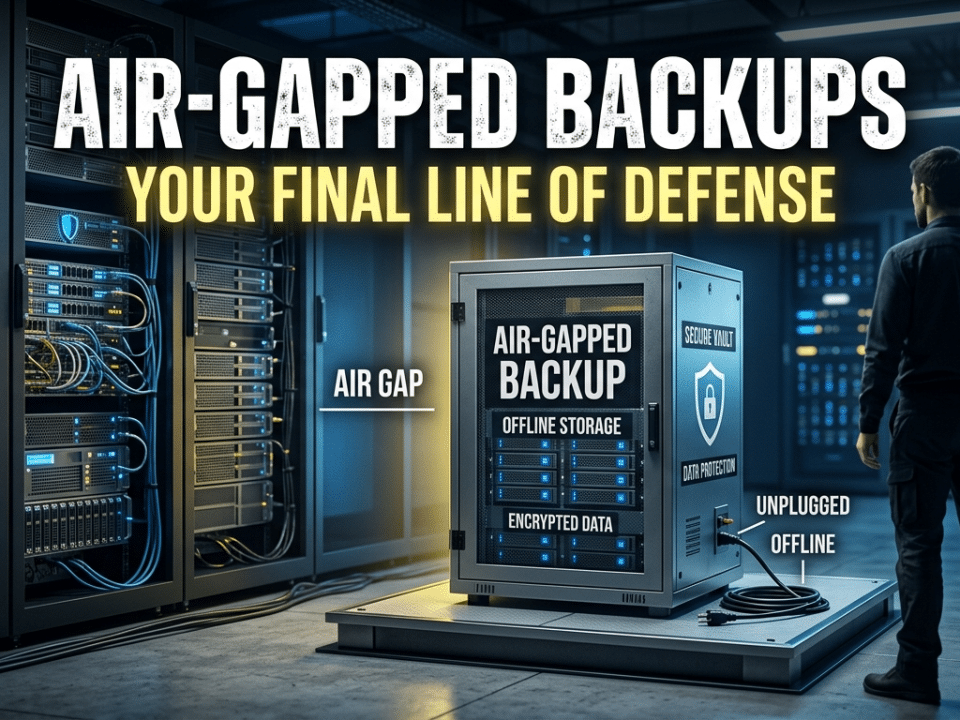
- CASB Implementation: We deploy Cloud Access Security Brokers. This acts as a “Gatekeeper” that monitors data as it moves between your network and the cloud, ensuring that sensitive data (like Social Security numbers or trade secrets) can never be uploaded to an unauthorized site.
Conclusion: Control Requires Visibility
In the 2026 Trust Economy, you cannot protect what you cannot see. If your security strategy ignores the “Shadows,” you aren’t actually secure—you’re just optimistic.
Is your data “Hiding” in the darkness? Contact Krypto IT today for a “Shadow IT Discovery Audit” and let’s bring your security into the light.