The 24/7 Digital Sentry: Why SIEM/SOC is Non-Negotiable
April 14, 2026
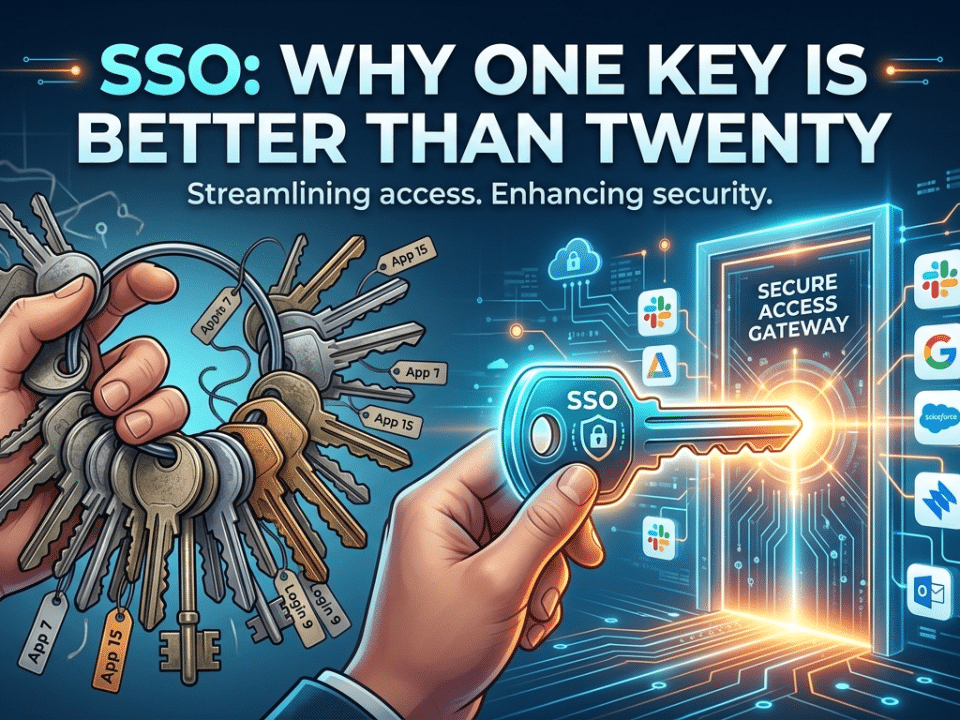
Why Your Growing Team Needs an IdP Now
April 16, 2026The Invisible Shield: Why Air-Gapped Backups are the Only Way to Survive Ransomware
The Contrarian’s Security Playbook by Krypto IT | Challenging Outdated IT Dogma in Houston
If you run a business in Houston—from the engineering firms in the Energy Corridor to the medical practices in the Texas Medical Center—you’ve likely been told the same thing for a decade: “As long as you have a backup, you’re safe from ransomware.” You probably have a sleek little drive plugged into your server, or perhaps you’re paying a monthly fee for a cloud service that “syncs” your files in real-time.
At Krypto IT, we’re here to deliver a reality check that your traditional IT provider might be avoiding: In 2026, a “connected” backup is often just a ransom payment waiting to happen.
If your backup is always connected to your network, it isn’t a safety net; it’s an target. To truly survive a modern ransomware attack, you have to stop trusting the “sync” and start embracing the Air-Gap.
The “Mirror” Trap: Why Your Cloud Sync is Failing You
The most common backup strategy in Houston today is real-time synchronization. You save a file, and it instantly “syncs” to the cloud. It’s convenient, it’s fast, and it’s a disaster in a ransomware scenario.
The Reality: Modern ransomware is designed to be “patient.” It doesn’t just encrypt your files the moment it enters your network. Instead, it sits quietly for days or weeks. It spreads through your network, finds your backup credentials, and—crucially—waits for you to “sync” your disaster.
When the ransomware finally triggers, it encrypts your local files. Your cloud service sees those “changes” and immediately syncs the encrypted, useless versions to your backup. You go to restore your data, only to find that your “safety net” is just a mirror of your encrypted nightmare. By trusting the “live” connection, you’ve effectively helped the hacker destroy your only way out.
The “Backup Hunter” Era
In 2026, ransomware has evolved into a “Backup Hunter.” Hackers know that their leverage disappears if you can restore your data. Therefore, the first thing a modern script does when it infiltrates a Houston law firm or logistics hub is hunt for “Mapped Drives” and “Network Shares.”
If your backup drive is visible as a “D:” or “Z:” drive on your computer, it is visible to the ransomware. The software will encrypt the backup first, ensuring you have no choice but to pay. If your backup can “see” your network, the ransomware can “see” your backup. To be truly safe, your backup must be digitally invisible.
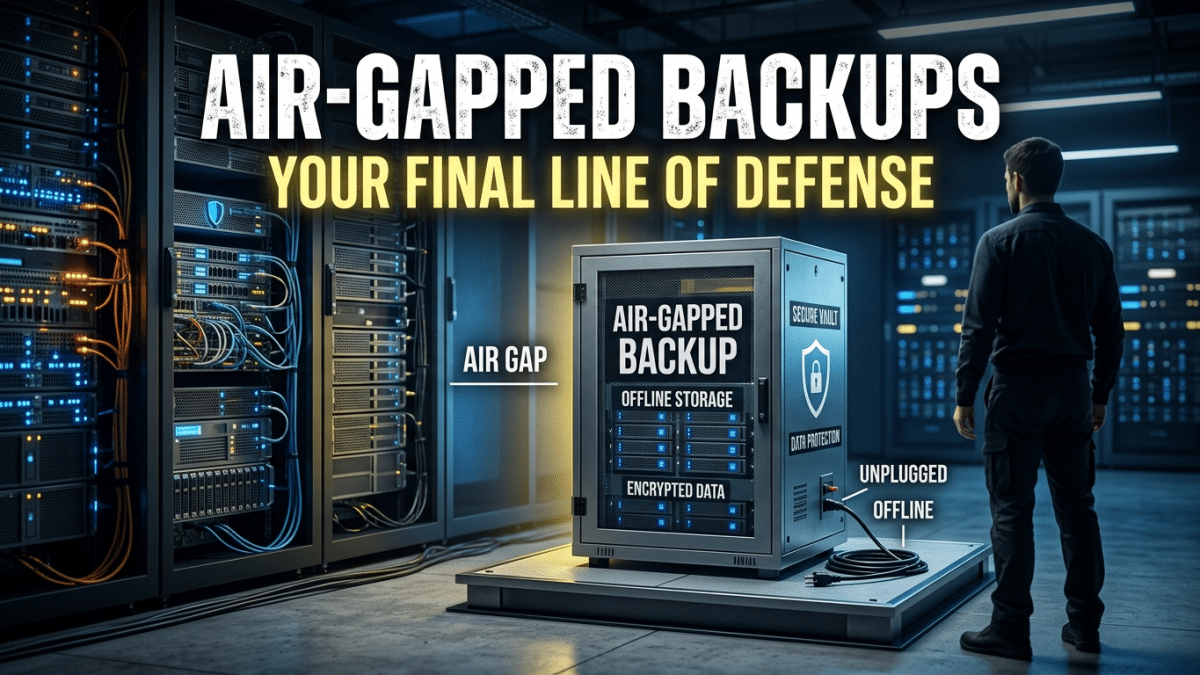
The Air-Gap: The Only True “Delete” Protection
An Air-Gapped Backup is a copy of your data that is physically or logically disconnected from your network. It is the digital equivalent of taking your most important documents and putting them in a safe that isn’t connected to the building’s alarm system.
The Contrarian View: In an era where everything is “connected” and “cloud-native,” the most sophisticated security move you can make is to go offline.
An air-gap ensures that there is a “gap of air” (or a non-routable logical break) between your production data and your recovery data. If a hacker takes over your entire network in Houston, they still cannot reach the air-gapped copy because there is no digital path to get there. They can’t encrypt what they can’t touch.
The Krypto IT “Immutable” Standard
We don’t believe “hope” is a backup strategy. Krypto IT implements a Triple-Tiered Recovery Architecture that prioritizes the gap:
- Immutability: We use “Write Once, Read Many” (WORM) technology. Even if a hacker finds the backup, the data is “locked” and cannot be changed or deleted for a set period, no matter how high their administrative privileges are.
- Logical Air-Gapping: We utilize specialized cloud vaults that require a separate, biometric-backed “handshake” to access. These vaults do not stay “mounted” to your network; they open briefly to receive data and then slam the door shut.
- The 3-2-1-1 Rule: We move beyond the traditional 3-2-1 backup rule by adding an extra “1”: One copy must be entirely offline and air-gapped.
Conclusion: Trust the Gap, Not the Wire
In the 2026 Trust Economy, your ability to recover from a disaster is what defines your brand’s resilience. If you are relying on a “sync” that a teenager in another country can intercept, you are building your business on sand.
Is your backup “Hunting Bait” for ransomware? Contact Krypto IT today for a “Data Resilience Audit” and let’s put some air between your business and the hackers.