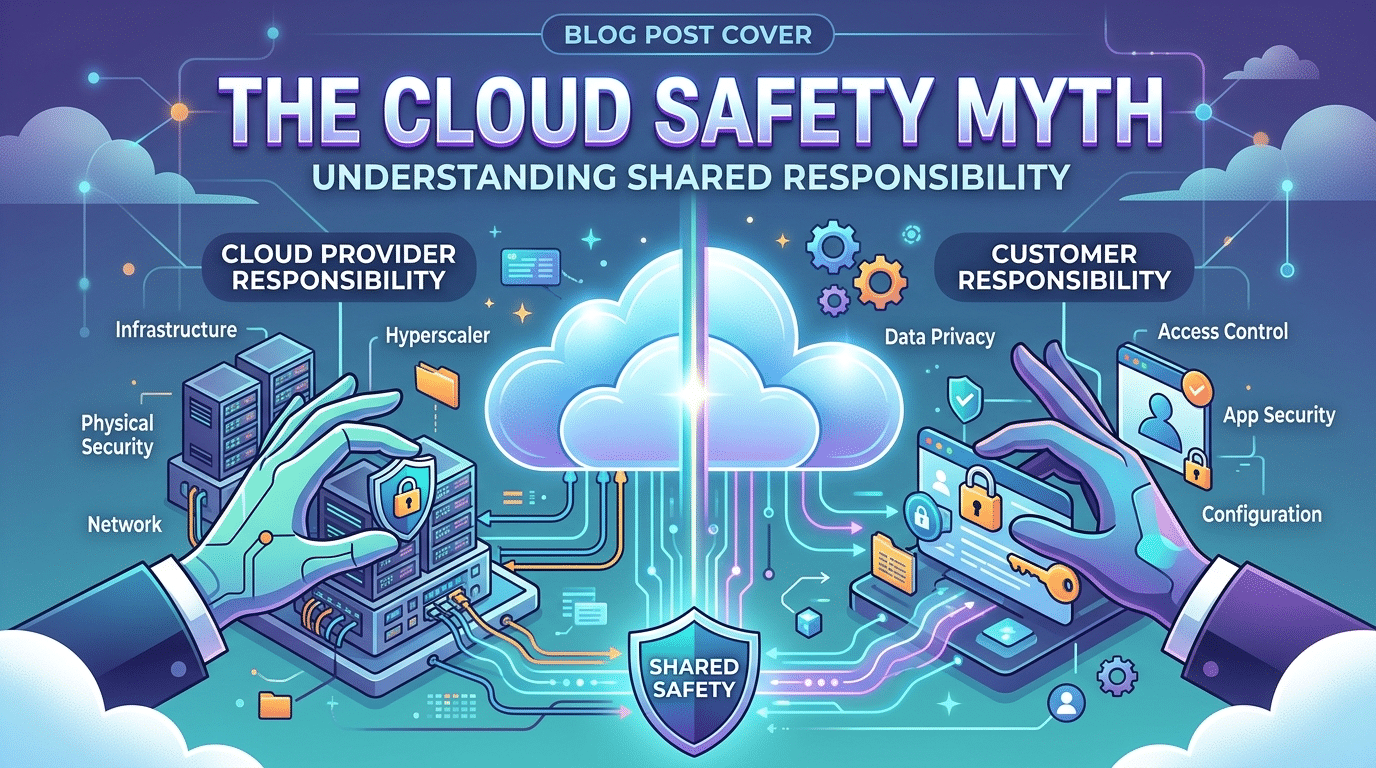
The Cloud Safety Myth: Understanding Shared Responsibility
April 1, 2026The Decay of the Snapshot: Why Point-in-Time Audits Fail to Protect Your Houston Firm
Security Lifecycle Intelligence Memo by Krypto IT | Advancing the Sentinel Standard in Texas
In the boardroom of a growing Houston firm—whether it’s a mid-sized engineering outfit in the Energy Corridor or a logistics giant near the Port—there is a common, comforting ritual: The Annual Security Audit. The consultant comes in, runs their scans, hands over a 40-page PDF of “Green Checks,” and the board breathes a collective sigh of relief. “We’re secure for the year,” they think.
At Krypto IT, we recognize this for exactly what it is: A dangerous illusion. In 2026, a one-time security audit is the digital equivalent of a physical exam taken once a decade. It tells you how you felt on a Tuesday morning in March, but it provides zero protection against the heart attack that occurs in October. This memo analyzes the “Decay of the Snapshot” and why continuous intelligence is the only true shield in a dynamic threat landscape.
1. The Security Obsolescence Rate (SOR)
Technology does not stand still. Every hour, new patches are released, new cloud configurations are changed by tired employees, and new zero-day vulnerabilities are discovered by hacking collectives. A “clean” audit report has a “Half-Life” that is shrinking every year.
If your “Monitoring Frequency” is once per year (the traditional audit), and your “Threat Velocity” (the rate of new exploits) is daily, your SOR is astronomical. By the time you’ve printed the results of your one-time audit, the data is already becoming obsolete. Within 30 days, a “Secure” network can become a “Target of Opportunity” simply through the natural entropy of software updates and user behavior.
2. The “Compliance vs. Security” Mirage
Many Houston firms confuse “Passing an Audit” with “Being Secure.” Audits are often designed around Compliance Frameworks (like SOC2, HIPAA, or CMMC). While these are essential, they represent the minimum standard of care.
The Intelligence Gap:
- The “Clean Room” Fallacy: During an audit, staff are on their best behavior. They follow protocols and close open ports. The moment the auditor leaves, the “Shadow IT” returns—personal devices are reconnected to the Wi-Fi, and “convenience” bypasses are re-enabled.
- The Static Threat Model: An audit tests for the threats that existed when the audit was written. It does not test for the polymorphic, AI-driven ransomware strains that will be born three months from now.
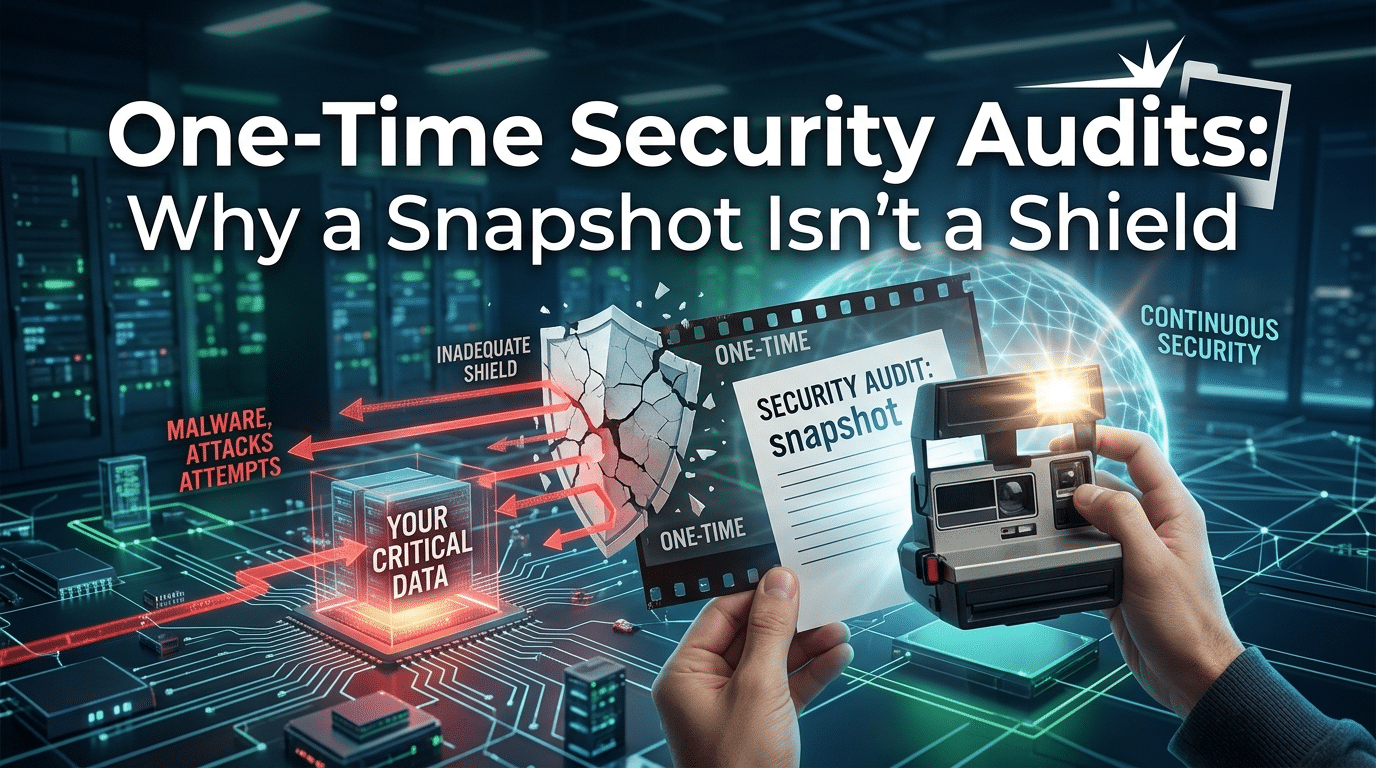
3. The “Polaroid” vs. The “Live Stream”
A one-time audit is a Polaroid. It’s a static, captured moment in time. It shows you the perimeter as it stood on a specific day.
In 2026, the hackers are using a Live Stream. They are using automated bots that scan your Houston-based IP addresses 24/7/365. They don’t care that you passed an audit in January if you have an unpatched vulnerability in July.
At Krypto IT, we believe in the “Sentinel Standard.” Instead of a static checkup, we provide a continuous “live stream” of security intelligence. Our Security Operations Center (SOC) doesn’t wait for an annual report; it hunts for anomalies in real-time, every single second of every single day.
4. The Human Entropy Factor
The most dynamic variable in your Houston business is your people. You can audit your technical controls, but you cannot “audit” the human element of security in a single day.
- New Hires: A “clean” audit doesn’t account for the three new employees hired in June who haven’t been trained on your phishing protocols.
- Departing Staff: A one-time audit won’t catch the “Orphaned Account” of a disgruntled former employee who still has remote access to your server.
- Configuration Drift: As your team “tweaks” the cloud settings for a new project, they unknowingly drift away from the secure baseline established during the audit.
How Krypto IT Implements Continuous Resilience
We don’t just “check boxes”; we provide the “Nervous System” for your security. Krypto IT replaces the useless one-time audit with a Continuous Resilience Cycle:
- Managed Detection and Response (MDR): 24/7/365 active threat hunting that never takes a “day off” between audits.
- Vulnerability Management as a Service: We don’t scan once a year; we scan continuously to find and patch holes as they appear.
- Dynamic Awareness Training: Security education that evolves as the threats evolve, keeping your “Human Firewall” current.
- Real-Time Compliance Reporting: Providing you with a “Live Dashboard” of your security posture so you always know where you stand.
Conclusion: Security is a Pulse, Not a Project
In 2026, the most successful firms in Houston treat cybersecurity as a vital sign—a constant pulse that must be monitored to ensure survival. A one-time audit is a project; true security is a lifestyle.
Is your firm’s safety based on a “Snapshot” from six months ago? Contact Krypto IT today for a “Dynamic Resilience Assessment” and let’s move beyond the check-the-box mentality.