Shadow IT: The Hidden Risk in Your Data
April 18, 2026The Ghost in the Machine: Why Dark Web Monitoring is the Only Way to Stop a “Quiet” Breach
The Contrarian’s Security Playbook by Krypto IT | Challenging Outdated IT Dogma in Houston
If you own a business in Houston—from the high-rise offices in the Museum District to the industrial complexes in Pasadena—you likely believe that a “breach” is a loud, chaotic event. You imagine sirens, locked screens, and a frantic call to your IT department. You think that if you haven’t seen a ransom note, you haven’t been hacked.
At Krypto IT, we’re here to deliver a chilling reality check: In 2026, the most dangerous breaches are the ones that make no sound at all.
While you are focused on building bigger walls, hackers are busy shopping. They aren’t “breaking in” to your network; they are “logging in” using credentials they bought for the price of a cup of coffee at a Heights-area cafe. If you aren’t actively monitoring the Dark Web, you are effectively flying blind through a digital storm.
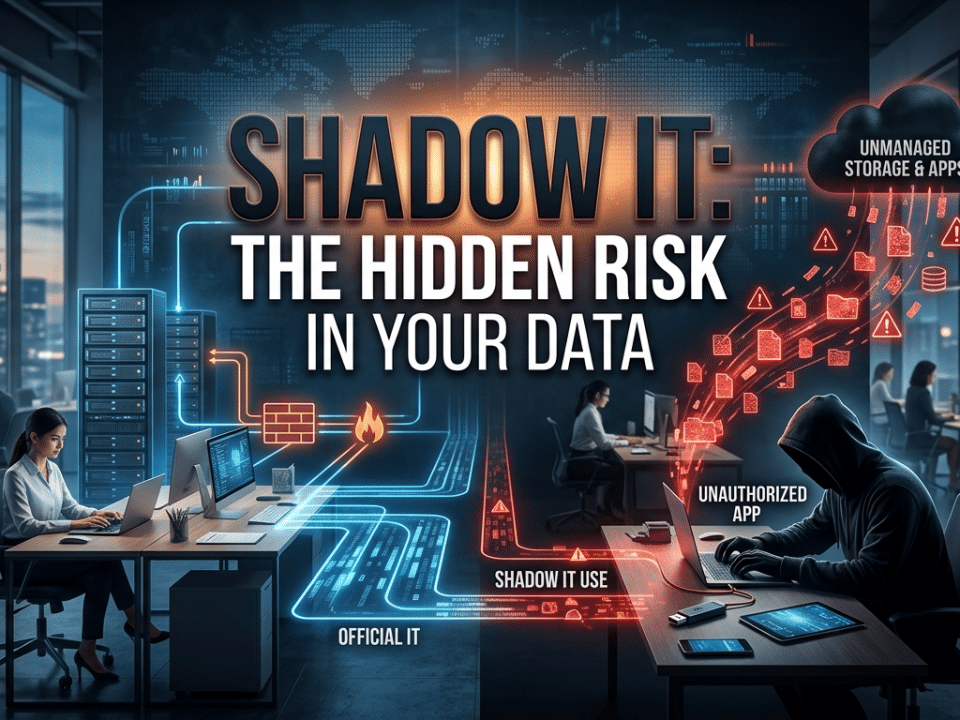
The “Ghost of Breaches Past”: Your Third-Party Vulnerability
The biggest myth in cybersecurity is that a leak of your company’s data has to come from your company.
The Contrarian View: Your employees are the weakest link, but not for the reason you think. Every time an employee uses their work email to sign up for a “professional” networking site, a local Houston food delivery app, or an industry-specific forum, they are creating a backdoor into your firm.
When those third-party sites get hacked—which happens thousands of times a year—your employee’s credentials (email and password) are harvested and dumped onto the Dark Web. If that employee “recycles” their password (and let’s be honest, 80% of them do), a hacker in another country now has the exact keys needed to log in to your Microsoft 365 or your VPN. You haven’t been “hacked” in the traditional sense; you’ve been traded like a commodity.
The Dark Web Marketplace: ROI for Hackers
To a business owner, the “Dark Web” sounds like a movie plot. To a cybercriminal, it’s a highly efficient marketplace with better customer service than most legitimate retailers.
Hackers don’t usually steal a password and use it immediately. Instead, “Initial Access Brokers” collect thousands of credentials, verify they work, and then bundle them into “Logs.” These logs are sold to “Ransomware-as-a-Service” groups who look for specific targets—like a mid-sized Houston engineering firm or a boutique law practice.
The Reality: By the time a hacker actually enters your network, your credentials may have been sitting on a Dark Web forum for six months. A one-time security audit will never find this. You need a Continuous Intelligence Loop that scans these marketplaces 24/7/365 to find your “keys” before the wrong person buys them.
Why “Hope” is Not a Security Strategy
Many Houston firms rely on the “I’ll know it when I see it” method of breach detection. They wait for a multi-factor authentication (MFA) prompt to pop up on their phone at 3:00 AM.
The Contrarian Problem: Sophisticated hackers now use “MFA Fatigue” attacks or “Session Hijacking” to bypass those prompts entirely. If they have your credentials from a leak, they are halfway through the door before your phone even buzzes.
Dark Web Monitoring isn’t about “stopping” a leak; it’s about Zero-Day Awareness. It gives you the “First Mover Advantage.” If we find your controller’s credentials on a new leak list at 2:00 PM on a Tuesday, we can force a password reset and rotate the security tokens before the hacker has even finished their cup of coffee. We turn a potential disaster into a 5-minute administrative task.
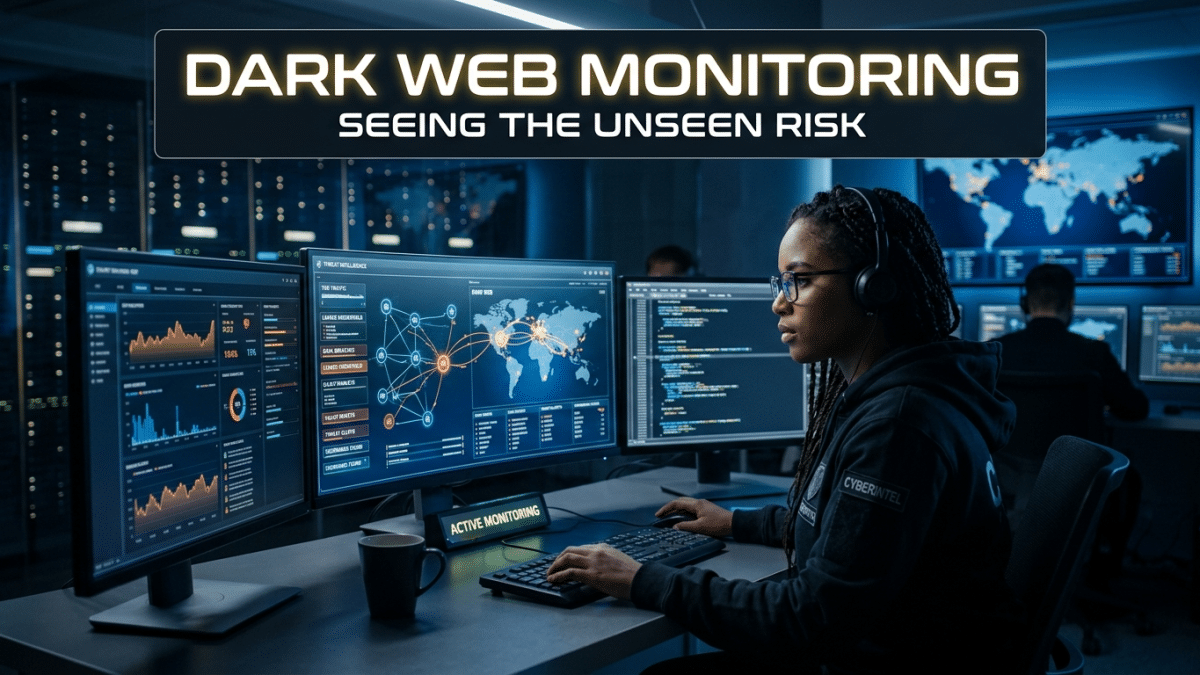
The Krypto IT “Sentinel Intelligence” Approach
We don’t believe in passive defense. Krypto IT provides an active “Radar” for your digital identity:
- Deep & Dark Web Scanning: We use specialized tools to scour unindexed corners of the internet, looking for any mention of your company’s domain or your employees’ emails.
- Instant Credential Revocation: The moment a match is found, our Security Operations Center (SOC) is alerted. We don’t just “report” it; we act—killing active sessions and hardening the account instantly.
- Historical Leak Analysis: We look at your firm’s “Digital Shadow” from the last decade, identifying old, leaked passwords that your team might still be using in some variation today.
- Supply Chain Monitoring: We don’t just watch you; we watch the third-party vendors and partners you rely on, ensuring their weakness doesn’t become your breach.
Conclusion: You Can’t Defend What You Can’t See
In the 2026 Trust Economy, your reputation is built on the things your clients don’t see. They expect you to be one step ahead of the predators. If you are waiting for the ransom note to arrive, you’ve already lost.
Are your company’s keys for sale right now? Contact Krypto IT today for a “Dark Web Exposure Report” and let’s reclaim your digital identity.