The Data Delusion: Ethics as a Growth Strategy
April 28, 2026The Long Shadow: A 100-Day Case Study of Life After a Cyber Breach in Houston
The Contrarian’s Security Playbook by Krypto IT | Challenging Outdated IT Dogma in Houston
If you listen to the marketing of most backup vendors, they’ll sell you a simple dream: “If you get hit by ransomware, we’ll click a button, restore your data, and you’ll be back to work by Monday morning.” It sounds clean. It sounds easy. It sounds like a problem solved.
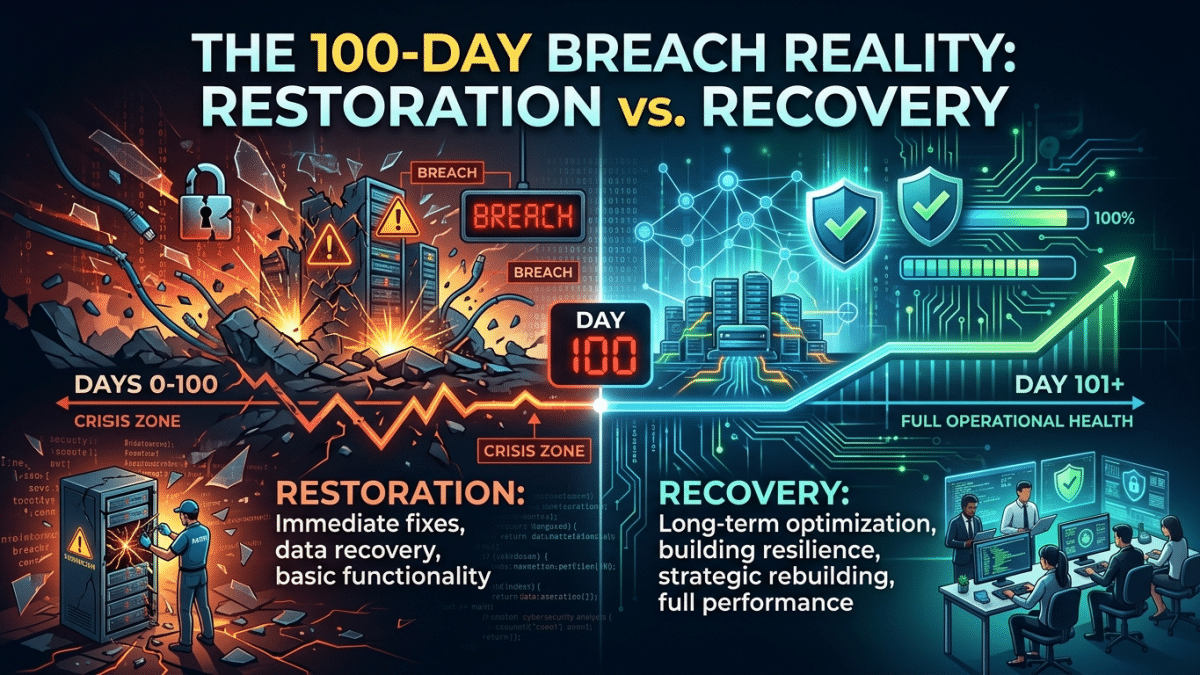
At Krypto IT, we’ve walked through the ashes with Houston firms, and we’re here to tell you the truth: Restoration is not recovery. Most business owners think the “crisis” is the week they spend without their servers. In reality, that’s just the first act of a three-act tragedy. The true test of your business happens on Day 100. By then, the news cameras are gone, the emergency IT team has sent their final bill, and you are left with the “Long Shadow” of the breach. This case study of a mid-sized Houston engineering firm reveals why the 100-day mark is where businesses either find a new baseline or begin a slow, silent collapse.
Day 1–15: The Expensive Sprint
The firm in our case study—let’s call them “Acme Engineering” based in the Energy Corridor—was hit by a polymorphic ransomware strain on a Friday. They had backups, so they thought they were safe.
The Reality: The first 15 days were a chaotic, high-priced sprint. Even with backups, it took 72 hours just to “clean” the environment so the ransomware wouldn’t re-infect the restored files. Total downtime was 10 business days. The “Visible Cost” was high—emergency labor, lost billable hours, and forensic fees. But the mood was optimistic: “We survived,” the CEO told the board.
Day 16–60: The Attrition of Trust
By Day 45, Acme Engineering was “fully operational” on paper. The servers were humming, and the emails were flowing. But beneath the surface, a silent rot had set in.
The Contrarian View: Clients don’t leave you the day you get hacked. They leave you 45 days later when they realize your “recovery” has made you slow, bureaucratic, and defensive.
Acme’s top three clients—major oil and gas players—didn’t cancel their contracts immediately. Instead, they began “Security Audits.” They demanded proof of new controls. They slowed down their payments while they “assessed the risk.” Acme’s project managers spent 40% of their time answering security questionnaires instead of designing infrastructure. This is the “Trust Tax,” and it’s a cost that never shows up on a traditional IT quote.
Day 61–90: The Internal Entropy
By month three, Acme’s “A-Players” began to leave. The breach had fundamentally changed the culture. To satisfy their insurance provider, Acme had implemented clunky, high-friction security measures that weren’t integrated into their workflow.
The employees felt like they were being punished for the breach. They were fighting with the tech every day just to open a CAD file. The best engineers—the ones who had options—moved to competitors who had “frictionless” security. By Day 90, Acme hadn’t just lost data; they had lost their competitive edge.
Day 100: The New Baseline
When we met with Acme on Day 100, the “Restoration” was long over, but the “Recovery” was still incomplete. Their profit margins had shrunk by 15% due to client attrition and increased administrative overhead. Their “un-hackable” backup had saved their files, but it hadn’t saved their brand.
The Lesson: Acme had a “Disaster Recovery” plan, but they didn’t have a “Sentinel Standard” of Resilience. They focused on the data instead of the business.
How Krypto IT Prevents the 100-Day Slide
We don’t just “restore files”; we engineer survivability. Krypto IT ensures that your Day 100 looks like “Business as Usual,” not “Business in Crisis”:
- Frictionless Security: we implement Zero-Trust and SASE models that protect your data without slowing down your A-Players. We make the “Right Way” the “Easy Way.”
- Reputational Readiness: We help you build a communication playbook so you can be transparent with clients before they start their own audits. You lead the conversation; they don’t drive it.
- Active Resilience Monitoring: We don’t just wait for a breach; we hunt for the “Quiet Signals” so the attack is neutralized before it even requires a “Restoration.”
- Operational Redundancy: We build “Parallel Infrastructures” that allow you to switch to a secondary environment in minutes, not days, ensuring your billable hours never stop.
Conclusion: Don’t Win the Battle but Lose the War
In the 2026 Houston market, your clients expect you to get hit. What they won’t forgive is if you let that hit turn you into a slow, unreliable partner. Restoration is a technical task; Recovery is a strategic victory.
Is your firm built for Day 100? Contact Krypto IT today for a “Resilience Case Study Audit” and let’s secure your long-term success.